To understand what quantum computing brings to the world of security, we must delve into how cryptography works, it’s facets including external actors and where this journey started from. Acknowledging the difference between classical cryptography and post-quantum cryptography will bring a somewhat improved outlook on cryptographic algorithms and allow for a process-demanding cryptography implementation. With this said, quantum computing solves the problems associated with conventional cryptography that are related to computational needs: the unrealistic processing demands on network devices such as firewalls and other smart clients configured to facilitate some level of security.
In today’s world of ever-increasing security threats and breaches, encryption is a common technique used to protect critical information from getting into the wrong hands. In cryptography, encryption is the process of encoding a plaintext message in such a way that only authorized parties can access it. The result of this process is encrypted information, also known as ciphertext. But how is this done exactly? The plaintext message is transformed using an algorithm (or cipher) to make it unreadable to anyone except those possessing special knowledge, which is referred to as the key.
Cryptography is the art of encoding and decoding messages. In short the design principle of cryptography is to make transmissible data meaningless to any party that is not required to read the message data. Classical cryptography achieves this by utilizing key distribution in which the encryption and decryption algorithms are publicly announced. Conventional cryptography consists of two techniques; secret key encryption (SKC) and public key cryptography (PKC). Security of the cryptogram is entirely dependent on the secrecy of the key. Obviously using a public channel no matter what precautionary measure are put in place is malleable. PKC systems exploits certain mathematical operations to encrypt data messages. Although PKC avoids the key distribution problem that is in SKC, it bases its security on unproven mathematical assumptions about the intrinsic difficulty of particular operations.
Since classical cryptography has proven flawed, it is paramount to have systems that can support the required levels of security to surpass modern threats. This is partly because for a long time traditional cryptography has been exploited. Even the once thought of as impenetrable Kerberos protocol has proven to be penetrable. Clearly as technologies take over our lives with Internet of Things, robotics and AI. There is a dire need to implement better crypto analysis algorithms to safeguard machines and its users.
Today, a hacker can passively intercept an encrypted message sent by "Alice" to "Bob" without either of them realizing that their message has been compromised. The hacker can do this in different ways, including fiber tapping, and can then spend lots of time and computing power to crack the code. The keys used in modern cryptography are so large that breaking the AES-256 standard would require “fifty supercomputers that could check a billion billion (1018) AES keys per second [and] would, in theory, require about 3×1051 years.” Thankfully this means that there isn't an immediate problem now, but what does the future hold when current computers are replaced with quantum computers? The keys that would take a trillion years to break with conventional computers could possibly be cracked in much less time with quantum computers. But there are putfalls.
The biggest pitfall associated with key distribution in conventional cryptography, is that this mode of security has no real monitoring safeguards. It assumes that decryption is not possible from an unknown party. Eavesdropping is simply not in the picture in both SKC and PKC. Therefore it is impossible to know whether interception of data messages while in transmission has occurred.
Quantum cryptography solves this problem well. Quantum Cryptography focuses on the introduction of new technologies that will offer more resistance to the computing power of quantum computers. Quantum cryptography draws its strength from the unpredictable nature of photons – the smallest particles in the universe. The foundation of quantum physics is defined by Heisenberg's Uncertainty Principle, which states that observation of these particles in any way changes their behavior. These new quantum cryptography technologies will combine the power of quantum physics and advanced mathematics to deliver maximum security.
The notion of an object having a superposition state is not science fiction with the discoveries of quantum mechanics. Physicist have proven this by realizing that the use of bits, which by the nature of their design are binary, cannot sustenance the fundamentals that quantum computing proposes. Bits are a simple two-state system, this is where classical cryptography inherits its problems from. In quantum computing, quibits (quantum bits) replace bits. Qubits are photons which can have multiple values such as “1”, “0” & “01”. Quibits are two-state quantum-mechanical systems with dynamic states of either being vertically polarized and/or horizontally polarized. The superposition of both states is fundamental in quantum computing.
Now, consider this same example leveraging quantum cryptography. Since we know we can't measure a photon without affecting its behavior, a hacker cannot go undetected when eavesdropping on a private message. After all of the photons are received by "Bob", and he and "Alice" have their conversation about the message transmitted, discrepancies will emerge if a hacker has intercepted the message. If this occurs, the 'transaction' can be aborted, and a new key sent automatically. By sending multiple quantum keys every second, the security of a fiber line can be constantly monitored and attempts to 'tap' the signal can be instantly identified.
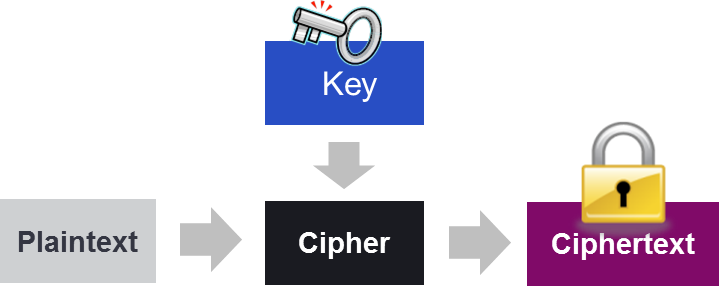
Basic Cryptography Model
As increasingly more sensitive information gets distributed across fiber-optic networks, today’s web-scale communications employ robust optical in-flight encryption solutions to ensure that data is secure, whether it is traveling across the city, across borders, or across the ocean. As the quantum compute era approaches, research and development advances in the area of cryptography are important to ensure that we will be able to continue to secure critical data and the network used to transport it across the globe.
Coming back to the key distribution problem in classical cryptography, quantum cryptography’s takes advantage of the superposition ability by changing the state of a quibit once eavesdropping has occurred. The Heisenberg Uncertainty principle or Quantum Entanglement brings the observe effect into the picture. This principle states that the measurements of certain systems cannot be made without affecting the system. Therefore eavesdropping on a photon’s properties cannot be done without changing its state. This is vital when it comes to quantum key distribution (QKD) and underlines the basis for overcoming classical key distribution eavesdropping monitoring or the lack thereof.
A key element of quantum cryptography that is being explored to guarantee secure communication is QKD. QKD uses photons to produce and distribute a key, not to transmit any message data. This key can then be used with any chosen encryption algorithm (like AES) to encrypt (and decrypt) a message, which can then be transmitted over a standard communication channel.
The main security benefit behind QKD is the ability of the two communicating parties to detect the presence of any third party trying to gain knowledge of the key. This is possible as a direct result of quantum mechanics whereby the process of measuring a quantum system in general disturbs the system changing the particles’ behavior. This means that a hacker trying to eavesdrop on the key must in some way measure it, thus introducing anomalies that can be detected and used to alert the parties that a key has been compromised and should not be used to encode information.
According to Born’s rule, the measurement outcome of a quantum state can be intrinsically random, which means that it can never be predicted better than blindly guessing. This key principle of quantum mechanics can be exploited by leveraging the inherent randomness in quantum measurements to generate true random numbers for highly secure cryptographic keys. These types of random number generators are referred to as Quantum Random Number Generators (QRNG) and are not new to the industry. Today, there are several QRNGs that are commercially available that promise true randomness to enable generating cryptographic keys that are impossible to predict.
Another area of Quantum Cryptography that is getting attention is Post-Quantum Cryptography (PQC), also called Quantum-Resistant or Quantum-Safe Cryptography. Essentially, this is research towards the development of new cryptographic algorithms that would be secure against the computational power of both quantum and classical computers. These next-gen algorithms will serve as replacements for our current public-key cryptosystems to prepare for the day when large-scale quantum computers become a reality. The National Institute of Standards and Technology (NIST) has already started to move in this direction with the kick-off of its Post-Quantum Crypto Project.
Currently Tapestry Digital Services is participating in this project. This project is a process to solicit, evaluate, and standardize one or more quantum-resistant public-key cryptographic algorithms. This is same type of process that was put in place by NIST years ago when it was searching for a new algorithm to replace the Data Encryption Standard (DES) published in 1977. This process resulted in the AES-256 encryption algorithm extensively deployed today. These new PQC standards will be used as quantum resistant counterparts to existing standards that are currently available.
It must be acknowledged that quantum cryptography is only used in the production and distribution of a key, not in the transmission of any messages. Another attribute that improves on classical key distribution in quantum computing is the exploitation of quantum mechanical properties of a quibit. Quibits cannot be copied or amplified without disturbing its original state as with the Heisenberg Uncertainty principle. This is known as the No-Cloning Theorem. This microscopic behavior of quantum computing building blocks, quibits, can be seen that the undeniable flaws of bits have led to the implementation of crypto systems with crypto analysis countermeasures that have been successful. Quantum cryptography proposes to revolutionize thi applying the laws of physics instead of mathematical algorithms to computing technology.
Areas Tapestry Digital Services are currently involved in are:
- The Internet of Things (IoT) - Are we ready for IoT to take over our social lives? What role with quantum computing and cryptography as well as Artificial Intelligence (AI) and the security concerns there play in all things IoT?
- AI Reality search engines.
- Bio and Nano IoT technologies - Monitoring things such as pacemakers, Blood Pressure, A1C, et al.
- Monitoring and Tracking - Embedded identification chips, Smart Dust, Nano-monitoring textiles, Wearbles, etc.
- Efficient Vehicles (EVs) and Automated Vehicles (AVs) - Quantum AI decision engines, GPS Security, In-vehicle security, In-vehicle monitoring (medical, safety, etc.) Safety overrides and backups, etc.
Granted there is still work to be done, the overhaul of the current bit system will not happen overnight. Technologies required to facilitate this transition, with the help of Moore’s Law is are coming closer than ever before. The future of quantum computing is exciting.
If you would like to know more about quantum cryptography or need to find out how the Tapestry's Security Team can complement or supplement your existing IT security portfolio, call us today and a member of our IT Security Team can walk you through your options and recommend a solution tailored just for your business needs so you can invest with confidence.